colanschwartz (@colanschwartz@mastodon.social)
#nextjs #security #vulnerability #infosec #cve #react #cybersecurity #cve #rsc #js #Javascript
Show Original Post
Sonnenbrand (@Sonnenbrand@chaos.social)
Da ich auf die schnelle keinen einfachen Moodttacker für #android gefunden habe, dem ich traue oder der aktiv entwickelt wird, habe ich versucht einen eigenen Tracker mit meinem Freund kAI zu bauen. Da Python für mobile Apps nur okayish ist, gings zu #react und dem Expo Framework. Problem ist das dieses Setup aktuell vom #fdroid build nicht unterstützt wird. Daher nun alles in den Play Store und oh my das ist ein Akt.
Show Original Post
TheServitor (@TheServitor@sigmoid.social)
Don't do this on someone else's system of course, but one could use #react2shell #cve with a payload that patches the issue 👀
I just attack-patched 19.1 in my VM 😂
$ py poke-react.py http://localhost:3000 'npm install next@15.5.7 --save'
Show Original Post
devto_vn_bot (@devto_vn_bot@mastodon.maobui.com)
Lỗ hổng CVE nghiêm trọng trong React đã bị công khai! Hãy kiểm tra và nâng cấp ứng dụng React của bạn ngay lập tức để đảm bảo an toàn. Đừng chần chừ, bảo mật là ưu tiên hàng đầu!
#React #ReactJS #Security #BảoMật #Vulnerability #LỗHổng #CVE
https://dev.to/drprime01/react-cve-vulnerability-exposed-check-out-how-to-secure-your-apps-now-bie
Show Original Post
Sempf (@Sempf@infosec.exchange)
You know that hacked up xkcd that gas the digital world balancing on a <tech>?
Now it needs recursion.
https://www.securityweek.com/cloudflare-outage-caused-by-react2shell-mitigations/
Show Original Post
heiseonlineenglish (@heiseonlineenglish@social.heise.de)
Patch now! Attacks on React2Shell vulnerability are starting
Due to ongoing attacks, admins should update their React servers promptly.
#Cyberangriff #Exploit #IT #React #Security #Sicherheitslücken #Updates #news
Show Original Post
leanpub (@leanpub@mastodon.social)
Frontend System Design Essentials: A practical guide to designing scalable, reliable, and maintainable frontend systems https://leanpub.com/frontend-system-design-essentials by Juntao Qiu is the featured book on the Leanpub homepage! https://leanpub.com #ComputerProgramming #React #WebDevelopment
Find it on Leanpub!
Show Original Post
fastlydevs (@fastlydevs@mastodon.social)
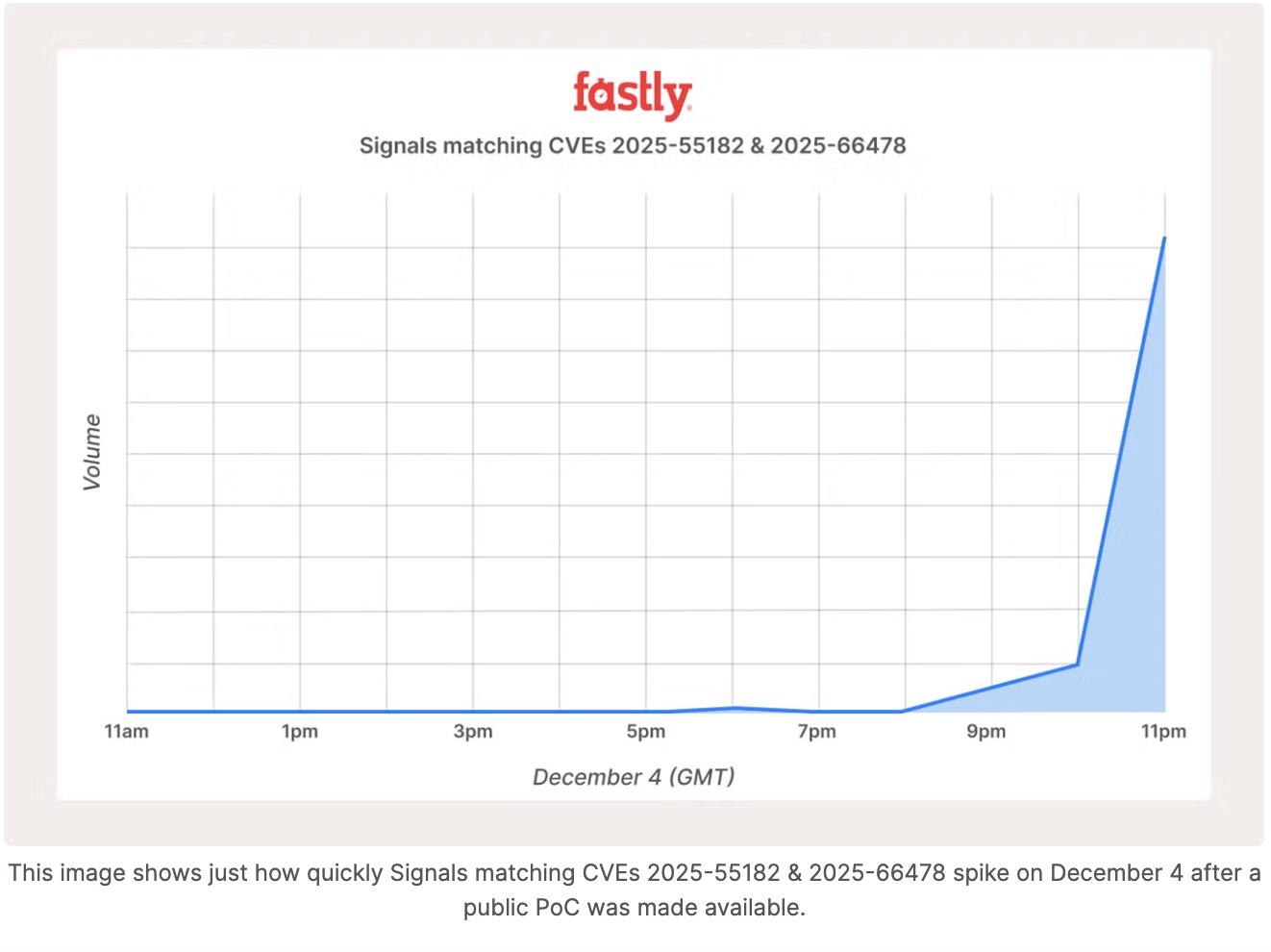
🚨 React2Shell Update – evening of Dec 4, 2025 🚨
After the public PoC for React2Shell (CVE-2025-55182 & CVE-2025-66478), exploit attempts spiked across our network. Patch React 19 & Next.js apps and enable the NGWAF Virtual Patch.
🔗 Full update: https://www.fastly.com/blog/fastlys-proactive-protection-critical-react-rce-cve-2025-55182
#React2Shell #CyberSecurity #NGWAF #AppSec #React #Nextjs
Show Original Post
AAKL (@AAKL@infosec.exchange)
New. Suffer the buffer.
The issue "was triggered by changes being made to our body parsing logic while attempting to detect and mitigate an industry-wide vulnerability disclosed this week in React Server Components."
"As part of our ongoing work to protect customers using React against a critical vulnerability, CVE-2025-55182, we started rolling out an increase to our buffer size to 1MB, the default limit allowed by Next.js applications."
Cloudflare: outage on December 5, 2025 https://blog.cloudflare.com/5-december-2025-outage/ @cloudflare #Cloudflare #infosec #React
Show Original Post
ml4den (@ml4den@social.vivaldi.net)
A critical zero-day in widely-used web frameworks sent shockwaves through the development community this week, with state-sponsored actors moving faster than most security teams could respond.
#react #nextjs #cloudflare #react2shell #cybersecurity
https://cybernewsweekly.substack.com/p/cybersecurity-news-review-week-49-fc4
Show Original Post
objects (@objects@twitter.oksocial.net)
RT by @SwiftOnSecurity: It’s wild how little sticks around when someone hits a server with the #React RCE payload. All the interesting parts of the POST request live for a moment in memory, get decoded, executed (or rejected), and vanish. Nothing hits a log, nothing lands on disk.
You can scan process memory for patterns, sure, but you’ll mostly catch scanners, broken requests, bots, random noise. A clean “this was a successful exploit” signal isn’t really possible here. The only reliable detection is post-exploitation activity on the box.
Super fun vuln to hunt for… not 😅
🐦🔗: https://nitter.oksocial.net/cyb3rops/status/1996994056153370860#m
[2025/12/05 17:24]
Show Original Post
AAKL (@AAKL@infosec.exchange)
New.
GreyNoise: CVE-2025-55182 (React2Shell) Opportunistic Exploitation In The Wild: What The GreyNoise Observation Grid Is Seeing So Far https://www.greynoise.io/blog/cve-2025-55182-react2shell-opportunistic-exploitation-in-the-wild-what-the-greynoise-observation-grid-is-seeing-so-far @greynoise #infosec #React #threatresearch
Show Original Post