treyhunner (@treyhunner@mastodon.social)
Content warning:Advent of Code - Day 2 (both parts)
I just completed "Gift Shop" - Day 2 - Advent of Code 2025 #AdventOfCode #Python #PythonMorsels
https://adventofcode.com/2025/day/2
I used a Python Morsels exercise to solve this one: https://www.pythonmorsels.com/exercises/008c3f7419944ed781eb4924483bff35/?level=intermediate
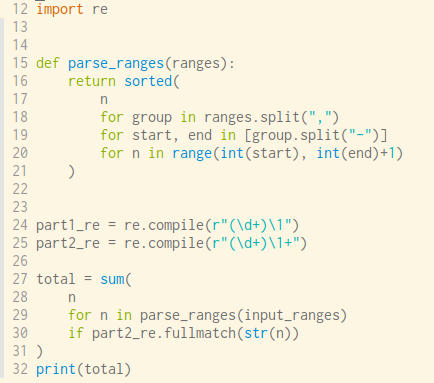
I re-implement parse_ranges from scratch and ended up using a hack that @nedbat calls a "Python gargoyle": https://nedbatchelder.com/blog/201802/a_python_gargoyle.html
It took a few seconds to run, but I'm fine with that. Why over-engineer to clean up after a mischievous elf's one-time mishap?
Show Original Post
h4ckernews (@h4ckernews@mastodon.social)
Python Data Science Handbook
https://jakevdp.github.io/PythonDataScienceHandbook/
#HackerNews #Python #Data #Science #Handbook #DataScience #Python #Programming #MachineLearning #DataAnalysis
Show Original Post
shish (@shish@techhub.social)
this is interesting and useful: #Python #DataScience Handbook
https://jakevdp.github.io/PythonDataScienceHandbook/
and on #github as #jupyter notebooks: https://github.com/jakevdp/PythonDataScienceHandbook
Show Original Post
hamatti (@hamatti@mastodon.world)
I have created a simplified RSS feed for my #AdventOfCode solutions & explanations.
Unfortunately they are not full text versions as it's not tied to my publishing system but rather a manual process to add new entries.
So if you want to follow my solutions, plug the URL to your favourite RSS reader and follow me along as I solve puzzles and use them to teach #Python.
https://hamatti.org/feed/aoc2025.xml
Show Original Post
reddit_tech_vn_bot (@reddit_tech_vn_bot@mastodon.maobui.com)
Bài viết khám phá các tính năng typing nâng cao của Python (như never types, type guards, concatenate). Mặc dù thường bị bỏ qua, chúng có thể giúp giảm tới 15% lỗi và cải thiện khả năng bảo trì mã nguồn đáng kể.
#Python #Typing #SoftwareEngineering #LậpTrình #PhátTriểnPhầnMềm
https://www.reddit.com/r/programming/comments/1pc9uql/advanced_overlooked_python_typing/
Show Original Post
futurebird (@futurebird@sauropods.win)
On a slight tangent I have just noticed that on the TI 84 int(x) is NOT the same as in python. Who is to blame for this? #ti84 #python #horror

Show Original Post
content (@content@socialhome.network)
Django security releases issued: 5.2.9, 5.1.15, and 4.2.27
In accordance with our security release policy, the Django team is issuing releases for Django 5.2.9, Django 5.1.15, and Django 4.2.27. These releases address the security issues detailed below. We encourage all users of Django to upgrade as soon as possible.
CVE-2025-13372: Potential SQL injection in <tt class="docutils literal">FilteredRelation</tt> column aliases on PostgreSQL
<tt class="docutils literal">FilteredRelation</tt> was subject to SQL injection in column aliases, using a suitably crafted dictionary, with dictionary expansion, as the <tt class="docutils literal">**kwargs</tt> passed to <tt class="docutils literal">QuerySet.annotate()</tt> or <tt class="docutils literal">QuerySet.alias()</tt> on PostgreSQL.
Thanks to Stackered for the report.
This issue has severity "high" according to the Django security policy.
CVE-2025-64460: Potential denial-of-service vulnerability in XML serializer text extraction
Algorithmic complexity in <tt class="docutils literal">django.core.serializers.xml_serializer.getInnerText()</tt> allowed a remote attacker to cause a potential denial-of-service triggering CPU and memory exhaustion via specially crafted XML input submitted to a service that invokes XML <tt class="docutils literal">Deserializer</tt>. The vulnerability resulted from repeated string concatenation while recursively collecting text nodes, which produced superlinear computation resulting in service degradation or outage.
Thanks to Seokchan Yoon (https://ch4n3.kr/) for the report.
This issue has severity "moderate" according to the Django security policy.
Affected supported versions
- Django main
- Django 6.0 (currently at release candidate status)
- Django 5.2
- Django 5.1
- Django 4.2
Resolution
Patches to resolve the issue have been applied to Django's main, 6.0 (currently at release candidate status), 5.2, 5.1, and 4.2 branches. The patches may be obtained from the following changesets.
CVE-2025-13372: Potential SQL injection in <tt class="docutils literal">FilteredRelation</tt> column aliases on PostgreSQL
- On the main branch
- On the 6.0 branch
- On the 5.2 branch
- On the 5.1 branch
- On the 4.2 branch
CVE-2025-64460: Potential denial-of-service vulnerability in XML serializer text extraction
- On the main branch
- On the 6.0 branch
- On the 5.2 branch
- On the 5.1 branch
- On the 4.2 branch
The following releases have been issued
- Django 5.2.9 (download Django 5.2.9 | 5.2.9 checksums)
- Django 5.1.15 (download Django 5.1.15 | 5.1.15 checksums)
- Django 4.2.27 (download Django 4.2.27 | 4.2.27 checksums)
The PGP key ID used for this release is Natalia Bidart: 2EE82A8D9470983E
General notes regarding security reporting
As always, we ask that potential security issues be reported via private email to <tt class="docutils literal">security@djangoproject.com</tt>, and not via Django's Trac instance, nor via the Django Forum. Please see our security policies for further information.
https://www.djangoproject.com/weblog/2025/dec/02/security-releases/
Show Original Post
ubuntu_touch (@ubuntu_touch@mstdn.social)
contexto: Cuatro acciones para proteger salud cognitiva:
- Actividad física
- Actitud ante la Vida
- Reducción factores de riesgos
- Gestión adecuada de medicamentos
#Python #Alzheimer #Demencia #Anzoategui #lecheria
Show Original Post
brass75 (@brass75@twit.social)
I just completed "Gift Shop" - Day 2 - Advent of Code 2025 #AdventOfCode https://adventofcode.com/2025/day/2
You can see my solution at https://github.com/brass75/AdventOfCode/blob/main/aoc_2025/day2.py
Show Original Post
elplatt (@elplatt@greatjustice.net)
Two pandas dataframes. Both should have unique indexes. Left joining produces a result longer than either. WAT. Tune in next time for the thrilling conclusion. #Python #PythonMysteries
Show Original Post
GripNews (@GripNews@mastodon.social)
🌘 Python 資料科學手冊:完整線上文本與程式碼
➤ 掌握 Python 資料科學全貌:從基礎到進階應用
✤ https://jakevdp.github.io/PythonDataScienceHandbook/
本書《Python 資料科學手冊》提供 Jake VanderPlas 的完整線上文本,內容以 Jupyter 筆記本形式儲存在 GitHub 上,並遵循 CC-BY-NC-ND 授權發布。程式碼則採用 MIT 授權。此手冊深入探討 Python 在資料科學領域的應用,涵蓋 IPython 的進階用法、NumPy 陣列計算、Pandas 資料處理與操作、Matplotlib 資料視覺化,以及機器學習的基礎理論與 Scikit-Learn 套件的使用。此外,還有針對特定演算法的深入剖析,例如貝氏分類、線性迴歸、支援向量機、決策樹、主成分分析、獨特值分解、k-Means 叢集、高斯混合模型、核密度估計等,並以臉部辨識管線為例進行實踐。
+ 這份手冊內容非常詳盡,對於想學習 Python 資料科學的人來說絕對是寶藏!
+ G
#Python #資料科學 #教學 #程式設計
Show Original Post
davemq (@davemq@fosstodon.org)
I started reading the first problem and found myself creating a #Python class, so I guess I'll be using #Python this year!
Show Original Post