sysadminszone (@sysadminszone@noc.social)
We've just released version 0.21.0 of Homebox! This release introduces some amazing new features and bug fixes.
As usual, a huge thanks to all of our #opensource #developers !
Read more here:
https://github.com/sysadminsmedia/homebox/releases/tag/v0.21.0
Show Original Post
radwebhosting (@radwebhosting@mastodon.social)
How to Generate a Full #VPS #Backup Using #rclone (Simple 3-Minute Guide) This article provides a detailed step-by-step description of how to generate a full VPS backup using rclone.
What is rclone?
Rclone is a powerful open-source command-line tool for managing files on cloud storage services and local storage. You can think of it as kind of like "rsync" (the popular file-copying tool), but specifically ...
Continued 👉 https://blog.radwebhosting.com/how-to-generate-a-full-vps-backup-using-rclone-simple-3-minute-guide/?utm_source=mastodon&utm_medium=social&utm_campaign=mastodon.social #googledrive #backups #onedrive #opensource
Show Original Post
linuxsolutions (@linuxsolutions@mastodon.social)
☁️ Transição do VMware para o Apache CloudStack: Alternativa open source que elimina custos de licenciamento! 🚀 Transforme sua TI em um ambiente mais lucrativo e competitivo. 👉 https://linuxsolutions.com.br/vmware-para-o-apache-cloudstack/?utm_source=dlvr.it&utm_medium=mastodon #CloudComputing #ApacheCloudStack #VMware #OpenSource

Show Original Post
blablalinux (@blablalinux@mastodon.blablalinux.be)
Dans cette vidéo 🎥, je vous montre comment installer et utiliser ffSend en quelques commandes seulement. C'est simple, rapide et super pratique ! 🔥 #Linux #OpenSource #tutoriel #astuce #informatique
👉 https://peertube.blablalinux.be/w/ke7S2nAEwcxpSUCEkGJadg
Une petite question pour vous ! 👇
Quel est votre outil en ligne de commande préféré pour optimiser votre flux de travail ? Dites-le-moi en commentaire ! 👇
Show Original Post
onetechnews (@onetechnews@mastodon.social)
#Seed-OSS: #ByteDance's #AI models released as #opensource
https://technewsro.blog/seed-oss-modelele-ai-de-la-bytedance-lansate-ca-open-source/

Show Original Post
XeroLinux (@XeroLinux@fosstodon.org)
G'day y'all
Will be streaming soon join us !
https://www.youtube.com/watch?v=wztvd3h-vbI
Show Original Post
xoron (@xoron@infosec.exchange)
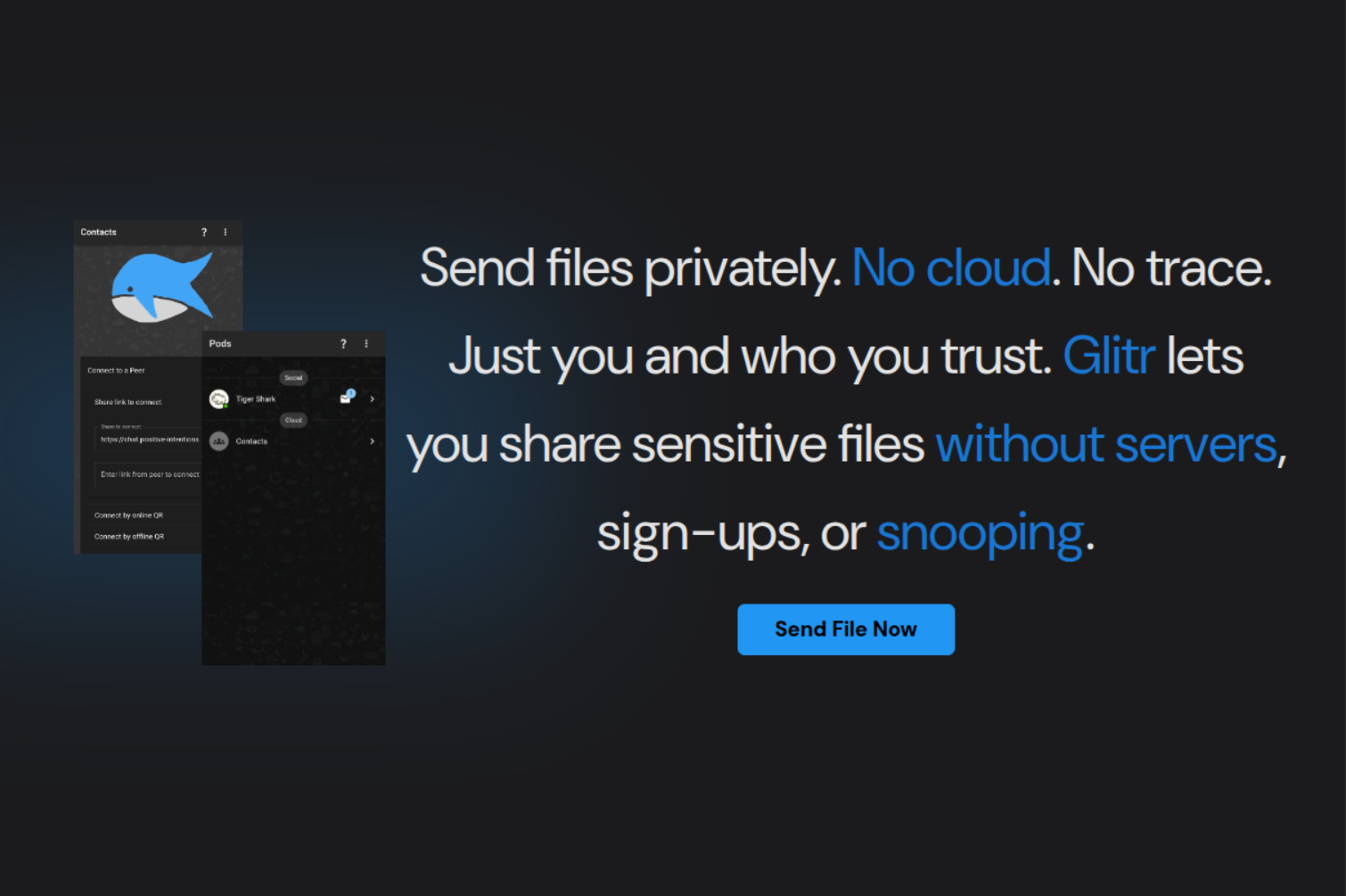
Send files privately. No cloud. No trace.
I’m working towards something for #secure / #private / #simple #P2P #filetransfer. It isnt as “simple” as it could be, im still working on it, but ive got it down to:
Zero-installation as a #PWA
Zero-registration by using local-only storage
#P2P-authentication using #WebCryptoAPI
Fast #datatransfer using #WebRTC, #syncthing, #croc, #sphynctershare and countless others. the key difference in my approach is that its a #webapp thats ready to go without any "real" setup process. you just need a browser.
I’m aware there are things like #SFTP and several other established protocols and tools. I started doing this because I was learning about #WebRTC and it seems suprisingly capable. This isnt ready to replace any existing apps or services.
(Note: I know you guys are typically interested in #opensource code. this project is a spin-off from a bigger project: https://github.com/positive-intentions/chat)
Let me know what you think about the app, features and experience you would expect from a tool like this.
---
SUPER IMPORTANT NOTES TO PREVENT MISLEADING:
These projects are not ready to replace any existing apps or services.
These projects are not peer-reviewed or security audited.
The chat-app is #opensource for transparency (as linked above)... but the file-app is not open souce at all (especially spicy when not reviewed or audited.).
All projects behind positive-intentions are provided for testing and demo purposes only.
Show Original Post
blog (@blog@kaspars.net)
Notes on FAIR Package Manager
Had a deeper look at the FAIR package manager today.
Right now the WordPress integration plugin doesn’t verify package signatures. That means WordPress sites can’t yet cryptographically confirm that a downloaded plugin or theme really came from the claimed publisher.
Verification isn’t trivial either. To check a did:plc identity properly you have to walk the entire chain of signed operations all the way back to the genesis operation. That’s where the DID is anchored.
That requires some pretty heavy crypto for a WordPress host (where the client plugin is installed):
- multibase / base58 decoding
- DAG-CBOR + CID recomputation
- ECDSA (secp256k1, P-256) signature checks
Not every shared host is going to have PHP extensions for all of that. The protocol does elegantly handle key rotation but the burden of verification falls entirely on the consumer.
Just “trusting” whatever keys come back from plc.directory for each package DID identifier isn’t secure. You have to validate the full audit log yourself because otherwise you’re open to tampering.
So the standard is promising but until FAIR bakes in real signature checks, WordPress users aren’t getting the security guarantees this model could deliver.
The rest of plugin features are really nice for privacy and general data protection — you no longer report all published content to Ping-o-Matic or send every admin dashboard request to WP-org servers. Here is a report of all external calls made by standard WordPress installs.
Show Original Post
xoron (@xoron@infosec.exchange)
Selhosted P2P E2EE File Transfer & Messaging PWA
https://positive-intentions.com
* #OpenSource
* #CrossPlatform
* #PWA
* #iOS, #Android, #Desktop (self compile)
* App store, Play store (coming soon)
* Desktop
* #Windows, #MacOS, #Linux (self compile)
* run `index.html` on any modern #browser
* #Decentralized
* #Secure
* #NoCookies
* #P2P #encrypted
* No registration
* No installing
* #Messaging
* Group Messaging (coming soon)
* Text Messaging
* #Multimedia Messaging
* #Screensharing (on desktop browsers)
* Offline Messaging (in #research phase)
* #FileTransfer
* #VideoCalls
* #DataOwnership
* #SelfHosted
* GitHub pages Hosting
* #LocalOnly storage
Check them out!
(Degoogled links to the apps)
- P2P Chat: https://chat.positive-intentions.com
- P2P File: https://file.positive-intentions.com
- Encrypted drive storage: https://dim.positive-intentions.com/?path=/story/usefs--encrypted-demo
- GitHub: https://github.com/positive-intentions
IMPORTANT NOTES (PLEASE READ!):
* These are NOT products. It's for #testing and #demonstration purposes only.
* They have NOT been reviewed or audited. Do NOT use for sensitive data.
* All functionality demonstrated is experimental.
* This is NOT meant to replace robust solutions like #VeraCrypt, #Simplexchat, #Signal, #Whatsapp, #wetransfer. It's just a #proofofconcept to show what's possible with #browser #APIs.

Show Original Post
p (@p@pixelfed.de)
Musik am Aachener Dom
#aachen #musik #music #cathedral #photo #photography #urbanphotography #livemusic #mastoart #art #streetart #streetphotography #reisefotografie #fotografie #foto #fotografia #lowlightphotography #travelphotography #fotografiadeviaje #opensource #opensourcesoftware #linux #gimp

Show Original Post
xoron (@xoron@infosec.exchange)
File Encryption with JavaScript.
I've been exploring the #WebCryptoAPI and I'm impressed!
When combined with the #FileSystemAPI, it offers a seemingly secure way to #encrypt and #store files directly on your device. Think #localstorage, but with #encryption!
I know #webapps can have #security vulnerabilities since the code is served over the web, so I've #OpenSourced my demo! You can check it out, and it should even work if #selfhosted on #GitHubPages.
Live Demo: https://dim.positive-intentions.com/?path=/story/usefs--encrypted-demo
Demo Code: https://github.com/positive-intentions/dim/blob/staging/src/stories/05-Hooks-useFS.stories.js
About the Dim framework:
https://positive-intentions.com/docs/category/dim
IMPORTANT NOTES (PLEASE READ!):
* This is NOT a product. It's for #testing and #demonstration purposes only.
* It has NOT been reviewed or audited. Do NOT use for sensitive data.
* The "password encryption" currently uses a hardcoded password. This is for demonstration, not security.
* This is NOT meant to replace robust solutions like #VeraCrypt. It's just a #proofofconcept to show what's possible with #browser #APIs.
#Encryption #Cryptography #JavaScript #Frontend #Privacy #Security #WebDevelopment #Coding #Developer #Tech #FOSS #OpenSource #GitHub #MastodonDev #Programming #WebStandards #FileSystem #WebAPI #ProofOfConcept

Show Original Post
techxperts (@techxperts@mastodon.social)
Tired of overpaying for Zapier/Make.com? 💸 Activepieces is the open-source hero for builders. Unlimited tasks, built-in AI agents 🤖, and full ownership when you self-host. No more task limits or vendor lock-in! #Activepieces #SelfHosted #Automation #OpenSource

Show Original Post