Amir_USBridge (@Amir_USBridge@social.tchncs.de)
Got tired of dragging a monitor to the rack just to get into the BIOS.
So I built a KVM that converts the firmware screen into live text — piped straight into an SSH terminal. Arrow keys inject HID keystrokes. No browser, no cloud, no video stream.
This is what it looks like in practice.
Pre-launch on Crowdsupply if anyone's curious: crowdsupply.com/usbridge-technologies/usbridge-kvm-2-0
#KVM #sysadmin #homelab #ssh #linux #openhardware #embedded
Show Original Post
royalapps (@royalapps@dotnet.social)
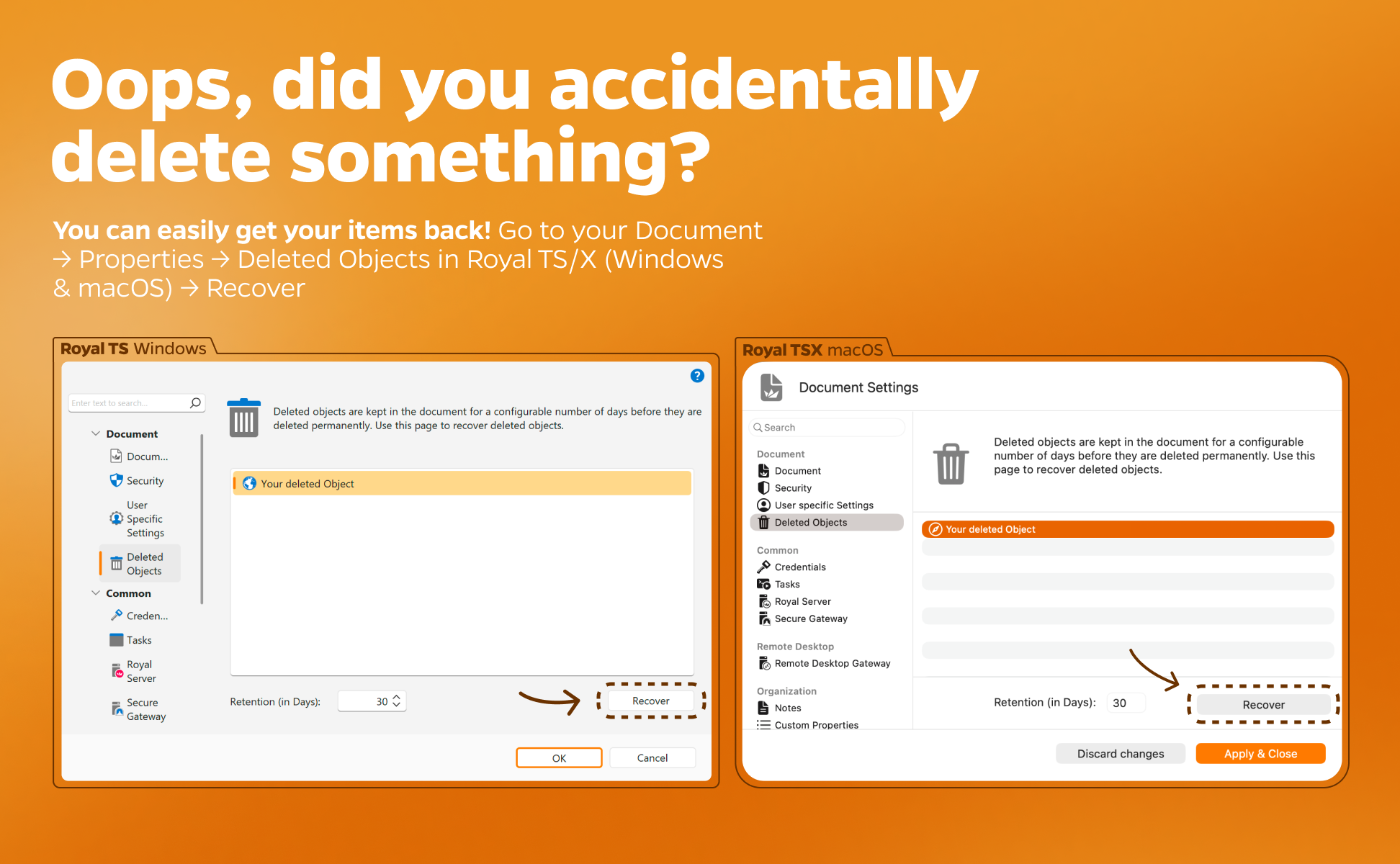
Oops, did you accidentally delete something? 🫣 You can easily get your items back! Go to your Document → Properties → Deleted Objects in Royal TS/X (Windows & macOS) → Recover ✨
#devops #itadmin #remotemanagement #RDP #msrdp #remotedesktop #azure #bastion #SSH #terminal #VNC
Show Original Post
techbot (@techbot@social.raytec.co)
Supply Chain Poisoning via PyPI Repository Compromise
Xinference, an open-source distributed AI model inference framework, suffered a supply chain attack when attackers compromised PyPI release credentials of maintainers and published three malicious versions (2.6.0, 2.6.1, 2.6.2) on April 22, 2026. The malicious code, encoded in Base64 layers within __init__.py, executes automatically upon library installation or import, collecting cloud credentials, SSH keys, API tokens, database passwords, cryptocurrency wallets, and environment variables. The payload specifically targets AWS environments through metadata service exploitation and uploads stolen data to attacker-controlled infrastructure. The attack affects users who downloaded these versions from PyPI, which has over 680,000 total downloads. Attribution remains unclear as TeamPCP's name appears in the code but the group denies involvement, suggesting third-party impersonation.
Pulse ID: 69ef4b48b61dcb4f48409e68
Pulse Link: https://otx.alienvault.com/pulse/69ef4b48b61dcb4f48409e68
Pulse Author: AlienVault
Created: 2026-04-27 11:40:56
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#AWS #Cloud #CyberSecurity #InfoSec #OTX #OpenThreatExchange #Password #Passwords #PyPI #RCE #SSH #SupplyChain #Troll #Word #bot #cryptocurrency #AlienVault
Show Original Post
techbot (@techbot@social.raytec.co)
AMOS Stealer delivered via Cursor AI agent session
On April 23, 2026, Field Effect MDR identified AMOS Stealer malware delivered through a novel technique exploiting Cursor AI agent sessions running Claude Code. The attack employed social engineering to manipulate operators into prompting the AI agent to download and execute malicious AppleScript loaders. The heavily obfuscated scripts performed sandbox evasion checks, collected sensitive data including credentials, SSH keys, browser data, and cryptocurrency wallets, then exfiltrated compressed archives to remote servers within two minutes. The malware prompted users for local account credentials through fake macOS system dialogs, subsequently using elevated permissions to install persistent implants masquerading as legitimate system services. This delivery mechanism makes detection challenging as malicious commands blend with typical agentic coding behavior, representing an evolution in AMOS Stealer tactics beyond traditional SEO poisoning methods.
Pulse ID: 69ec44ff58f20f2cb01e0a1c
Pulse Link: https://otx.alienvault.com/pulse/69ec44ff58f20f2cb01e0a1c
Pulse Author: AlienVault
Created: 2026-04-25 04:37:19
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#AMOS #Browser #CyberSecurity #ICS #InfoSec #Mac #MacOS #Malware #OTX #OpenThreatExchange #RAT #SEOPoisoning #SSH #SocialEngineering #bot #cryptocurrency #AlienVault
Show Original Post
pitrh (@pitrh@mastodon.social)
BSDCan https://www.bsdcan.org/2026/ Talk Friday 2026-06-19: 15:45 - 16:35 DMS 1110
Geographically fault-tolerant SSH on OpenBSD
Rob Keizer
https://www.bsdcan.org/2026/timetable/timetable-Geographically-fault-tolerant-SSH.html
To register https://www.bsdcan.org/2026/registration.html @bsdcan #openbsd #ssh #faulttolerance
Show Original Post
kushal (@kushal@toots.dgplug.org)
Who all in my timeline regularly using #git commit sign using smartcards and #openpgp? or doing #ssh using OpenPGP authentication subkey
Show Original Post
w (@w@watch.linuxrenaissance.com)
Waypipe in Action: Wayland Remote GUI Over SSH
https://watch.linuxrenaissance.com/w/5zNPh3NcCXLyrDKWAxUqF5
Show Original Post
w (@w@fediverse.tv)
Resumen de la Clase de SSH en el curso de terminal GNUlinux
https://fediverse.tv/w/kojxaSNibReRkf3E4RSKxg
Show Original Post
jean_dupont (@jean_dupont@mastodon.social)
Colors are nearly unchanged but the TUI over #ssh is now buttery smooth. 😄

Show Original Post
ssh-o-sftp-cosa-cambia-e-quale-usare-sul-tuo-server (@ssh-o-sftp-cosa-cambia-e-quale-usare-sul-tuo-server@emanuelegori.uno)
SSH o SFTP: cosa cambia e quale usare sul tuo server
SSH e SFTP fanno cose diverse. Scopri quando usare l'uno o l'altro e come configurarli correttamente sul tuo server self-hosted.https://emanuelegori.uno/ssh-o-sftp-cosa-cambia-e-quale-usare-sul-tuo-server/
Show Original Post
RedPacketSecurity (@RedPacketSecurity@mastodon.social)
CVE Alert: CVE-2026-7039 - tufantunc - ssh-mcp - https://www.redpacketsecurity.com/cve-alert-cve-2026-7039-tufantunc-ssh-mcp/
#OSINT #ThreatIntel #CyberSecurity #cve-2026-7039 #tufantunc #ssh-mcp
Show Original Post
MrKidney (@MrKidney@norden.social)
Ha! Hab nun einen Weg gefunden mit mehreren via Internet mit LibreOffice gemeinsam an einer Datei zu arbeiten 🙂. Es ist ein kleiner Umweg (eigentlich aber auch nicht), ich hab uns allen (Windows & Linux-Nutzer) ein SSH/SFTP Netzlaufwerk von meinem Server erstellt und in den Systemen eingehängt. Nun kann man quasi die Datei bei sich "lokal" in dem Netzlaufwerk speichern & laden was jedoch auf dem Server ist 🙂.
#linux #windows #libreoffice #zusammenarbeit #ssh #sftp #server
Show Original Post